Kernel Panic or Quiet Genius Computer Trivia







Quiz Complete!
Kernel Panic or Quiet Genius: The Tiny Decisions That Shaped Modern Computing

Most people experience computers as polished apps and fast websites, but the real drama happens in the layers you only notice when something breaks. A kernel panic, a blue screen, or a frozen VM is often the visible tip of a long chain of design tradeoffs: choices about memory layout, instruction sets, timing, and standards that were made decades ago and still echo today.
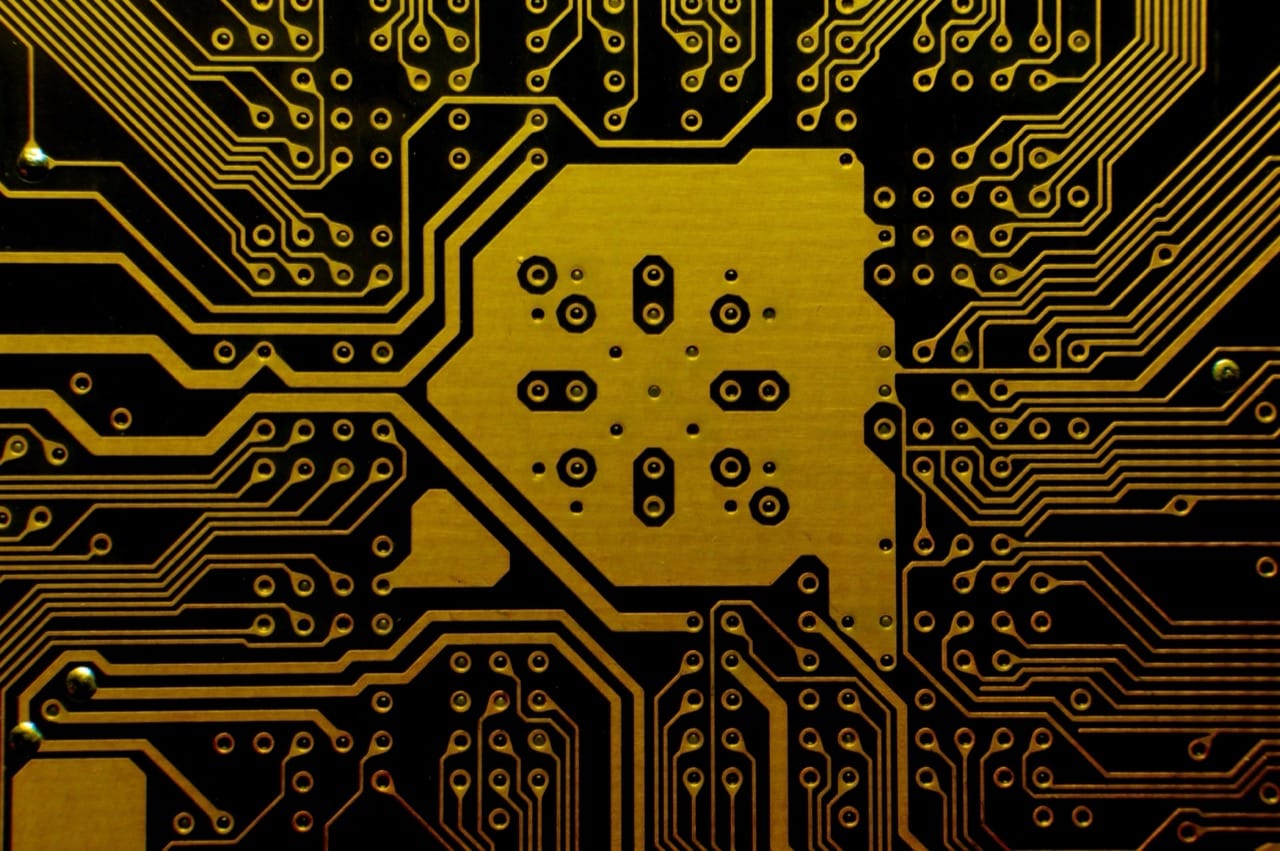
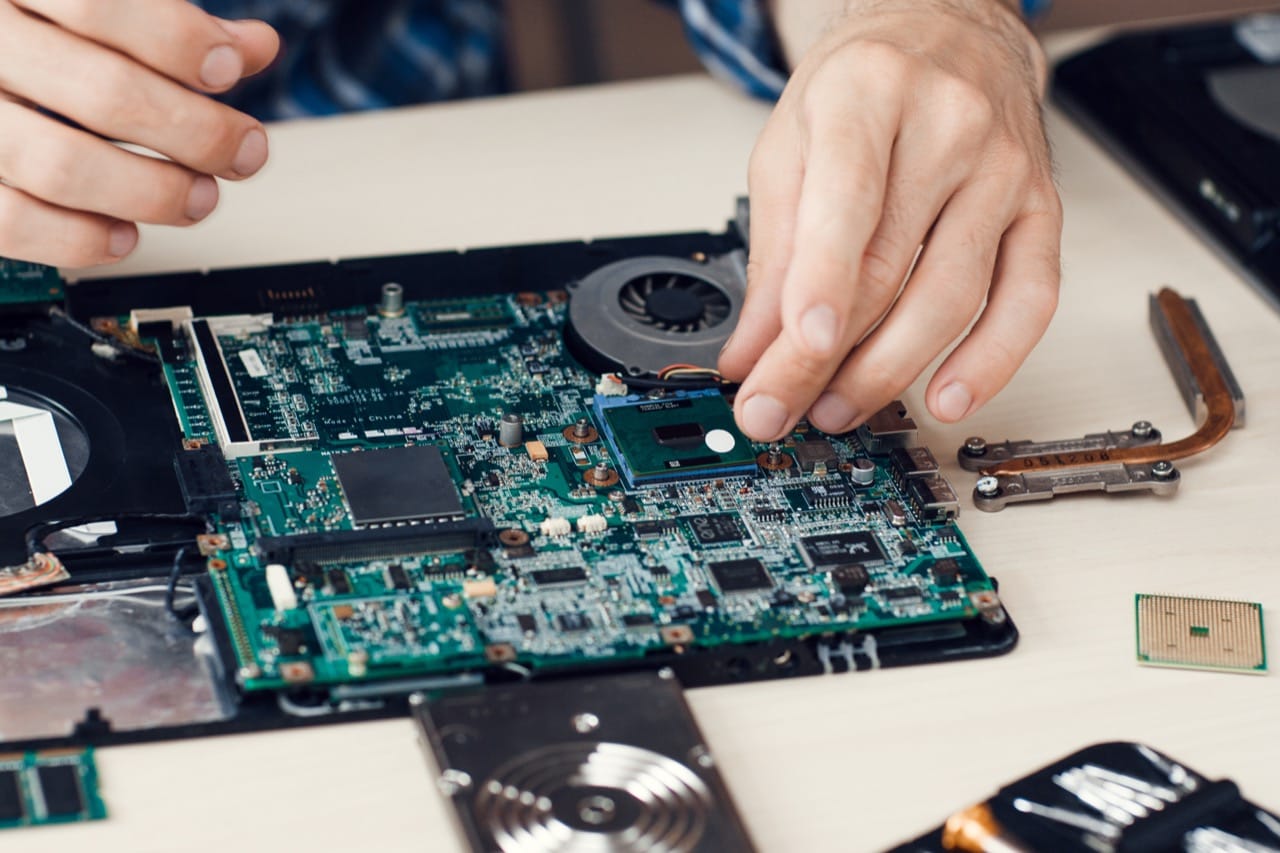
Consider the CPU itself. Early microprocessors like the 6502 and Z80 were constrained by cost and pin counts, which pushed clever compromises in addressing modes and bus design. Later, the RISC versus CISC debates were never about one side being smart and the other being wrong; they were about where complexity should live. Modern x86 chips still decode dense CISC instructions into simpler internal operations, effectively running a RISC-like engine behind the scenes. Even the floating point rules that many programmers treat as mysterious are formalized in IEEE 754, which defines NaNs, infinities, rounding modes, and the surprising fact that some arithmetic can be non-associative due to rounding. That standard enabled portability, but it also made room for tricky bugs when code assumes real-number math.
Operating systems hide another set of quiet genius. Virtual memory is not just extra RAM; it is a contract that lets processes pretend they have contiguous address space while the kernel maps pages to physical memory and disk. Page faults, copy-on-write, and memory-mapped files are performance tools as much as abstractions. File systems are similar: a filename is not the file. Many systems separate directories from inodes, track metadata independently, and rely on journaling or copy-on-write to survive crashes. The difference between a system that loses data after a power cut and one that recovers cleanly often comes down to ordering guarantees, write barriers, and whether the storage device lies about flushing caches.
Networking trivia is full of standards battles and pragmatic hacks. Ethernet’s original collision handling mattered more when hubs were common; modern switched networks changed the game, but the legacy remains in frame formats and assumptions. TCP is famously reliable, yet it cannot promise perfect delivery in all cases; it guarantees ordered bytes as long as both endpoints and the path cooperate, and it uses congestion control to avoid collapse. DNS looks simple until you meet caching, TTLs, recursive resolvers, and the fact that many failures are not about names at all but about timeouts and negative caching. Even the humble MTU can shape performance, because fragmentation and path MTU discovery affect how packets survive the real internet.
Security fundamentals often hinge on precise terms. Authentication is not authorization. Encryption is not integrity. Random-looking is not random enough. Timing attacks exploit tiny differences in code paths, which is why constant-time comparisons matter for secrets. Sandboxing and virtualization can reduce blast radius, but they rely on hardware features like rings, page tables, and IOMMUs, and they bring their own escape risks. Meanwhile, a single misconfigured permission bit or an overlooked deserialization path can undo a fortress of crypto.
Programming languages carry their own archaeology. C’s undefined behavior is not a bug in the spec; it is a performance bargain that lets compilers assume impossible things and optimize aggressively. Managed runtimes trade predictable memory safety for the complexity of garbage collection, JIT compilation, and warm-up effects. Even something as ordinary as a newline differs across history, and those differences still surface when tools meet old data.
The most satisfying computer trivia is rarely about memorizing dates. It is about recognizing that modern systems are layered agreements between hardware, software, and people, and that every layer contains tiny, sometimes odd decisions that turned out to be either a ticking time bomb or a stroke of quiet genius.